Overview
Whether you understand cloud computing or not, if you are savvy enough to use a smartphone or a laptop, chances are you already use cloud computing services. For example, if you have used Amazon.com, any Google Application, Microsoft 365 Suite, or even streamed movies and songs online, you have used cloud computing services.
Microsoft defines cloud computing as the “delivery of computing services—including servers, storage, databases, networking, software, analytics, and intelligence—over the Internet (“the cloud”) to offer faster innovation, flexible resources, and economies of scale. You typically pay only for cloud services you use, helping you lower your operating costs, run your infrastructure more efficiently, and scale as your business needs change.” Basically, companies can use the services mentioned above through the internet in place of their on-premise server.
So what brought about this cloud migration?
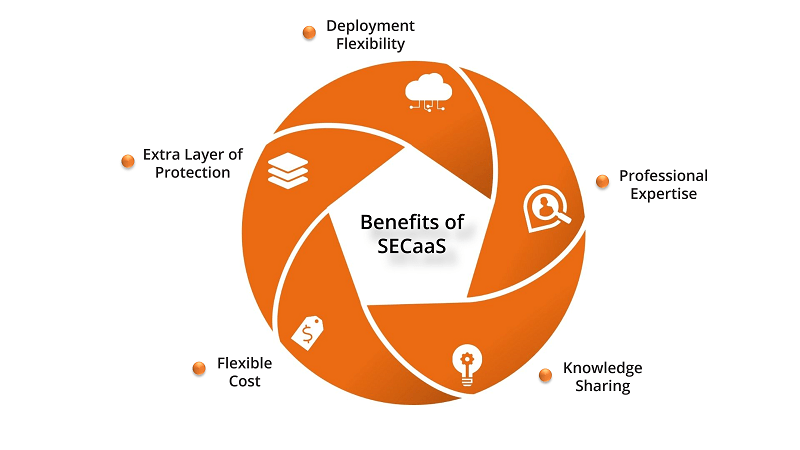
Due to lower operating costs and other efficiency factors, most companies, no matter their size, are quickly migrating to the cloud. This has led to many criticalities arising in the management of cloud architecture. Specifically, the security aspect needs utmost attention, mainly in application domains where integrity, privacy, and confidentiality of information must be guaranteed. SECaaS in cloud computing helps you achieve that.
Types of SECaaS
A lot of work has been done regarding the security of the cloud and the data within it. However, there was still a dearth of best practices guidelines to follow during developing and implementing an elastic cloud model. The Cloud Security Alliance (CSA) solved this problem by breaking the SECaaS into various categories:
Identity and Access Management (IAM)
IAM provides controls for access intelligence, identity verification, and access management. It includes processes, such as provisioning/de-provisioning of accounts, directory services, authentication, token management, etc.
THREATS ADDRESSED:
- Identity theft
- Unauthorized access
- Privilege escalation
- Insider threat
- Non-repudiation
- Excess privileges / excessive access
- Delegation of authorizations/entitlements fraud
Data Loss Prevention
This preventive measure mainly ensures that data (structured and unstructured) remains under control.
It deals with data security, monitoring, protection, and verification in the cloud and on-premises. Its functionalities include- data labeling & classification, identification of sensitive data, Structured data matching, SQL regular expression detection etc.
THREATS ADDRESSED:
- Data loss/leakage
- Unauthorized access,
- Malicious compromises of data integrity
- Data sovereignty issues
- Regulatory sanctions and fines
Web Security
This is a reactive and real-time protection mechanism against online applications offered via the cloud by redirecting web traffic to the cloud provider. It provides services like web filtering, spyware & bot network analyzer, phishing site blocker, email security etc.
THREATS ADDRESSED:
- Keyloggers
- Domain Content
- Malware
- Spyware
- Bot Network
- Phishing
- Virus
- Bandwidth consumption
- Spam
Email Security
Email security pertains to keeping the organization secure from malicious emails. It gives you complete control over the company emails, allowing you to set policies, encrypt communication, and block spam emails, among others.
THREATS ADDRESSED:
- Phishing
- Intrusion
- Malware
- Spam
- Address spoofing
Security Assessments
These are audits of cloud services or assessments of on-premises systems via cloud-provided solutions generally done by third parties. Some of the features are Risk management, compliance, technical compliance audits, application security assessments, etc.
THREATS ADDRESSED:
- Inaccurate inventory
- Lack of continuous monitoring
- Lack of correlation information
- Lack of complete auditing
- Failure to meet/prove adherence to Regulatory/Standards Compliance
- Insecure / vulnerable configurations
- Insecure architectures
- Insecure processes/processes not being followed
Intrusion Management
This process uses pattern recognition to detect and react to statistically unusual events to stop/prevent an intrusion in real-time. Generally, it provides identification of intrusions & policy violations, automatic/manual remedy actions, and updates to address new vulnerabilities & exploits.
THREATS ADDRESSED:
Security, Information and Event Management (SIEM)
This is a detection process in which the systems accept log/event information. This information is then analyzed and used to report and alert on events that may require intervention. It provides real-time log & event correlation, forensic support, log normalization, compliance reporting, etc
THREATS ADDRESSED:
- Insecure Interfaces and APIs
- Malicious Insiders
- Shared Technology Issues
- Data Loss and Leakage
- Account or Service Hijacking
- Unknown Risk Profile
- Fraud
- Abuse and Nefarious Use
Encryption
This process makes the data indecipherable by managing encryptions, hashing, digital signatures, and key exchanges. Its functionalities include- data protection, data validation, message authentication, data time-stamping, code signing, forgery detection, etc.
THREATS ADDRESSED:
- Failure to meet Regulatory Compliance requirements
- Mitigating insider and external threats to data
- Intercepted clear text network traffic
- Clear text data on stolen/disposed of hardware
- Reducing perceived risks
Network Security
Network Security refers to various services that help in distributing, managing, and monitoring security controls in a network. The functionalities are traffic/NetFlow monitoring, security monitoring, data threats, access control threats, security gateways, DoS protection/mitigation etc
THREATS ADDRESSED:
- Data Threats
- Access Control Threats
- Application Vulnerabilities
- Cloud Platform Threats
- Regulatory, Compliance & Law Enforcement

Product Engineering Services Customized software development services for diverse domains
Sustenance Engineering Going beyond maintenance to prolong life of mature products
Managed Services Achieve scalability, operational efficiency and business continuity
Technology Consulting & Architecture Leverage the extensive knowledge of our Domain Experts